OT vs. IT Network Design
Why Industrial Networks Need Their Own Rules
April 27, 2026
OT networks can look a lot like IT networks on paper: Ethernet, IP, VLANs, you name it. But in practice, they solve very different problems.
IT is organized around people, rapid change, and information flow.
OT is organized around machines, predictable timing, safety, and long equipment lifecycles.
Those differences change every design choice, from how you segment to what you can patch to how you control remote access. When designers treat OT like IT, small changes turn into production outages and short‑term fixes turn into long‑term debt. This guide will highlight the practical differences between OT and IT and lay out a clear path toward OT-first design for your operations.
What “Good” Means in OT vs. IT
Every network is built around a set of priorities. The right design for a corporate campus looks nothing like the right design for a production floor, because what "working well" means is completely different.
OT networks optimize for operations. That means they have to be reliable, predictable, and capable of containing failures before they spread. Safety, uptime, and deterministic communication aren't aspirational, they’re the baseline. When an OT network fails, the impact is immediate and measurable.
IT networks optimize for users and information. Enterprise IT is built around user access, business application availability, identity management, and the ability to move quickly. Systems get refreshed on predictable cycles, downtime can be scheduled, and patching is routine and expected.
Neither model is “wrong,” but applying IT priorities to OT environments introduces risk that doesn't always surface right away—and when it does, it tends to show up at exactly the wrong moment.
Network Design Constraints: OT vs. IT
The gap between OT and IT design isn't just philosophical. It shows up in specific constraints that shape every architectural decision, whether you're aware of them or not.
Change control and downtime windows
In IT, change is a normal part of operations, meaning brief disruptions are tolerable. Configurations get updated, patches get applied, and systems get upgraded on a regular basis. In OT, change carries real operational risk. Production schedules are tight, and maintenance windows are rare and carefully coordinated.
If you’re lucky, a configuration change may just slow you down. More often than not, it actually ends up halting a line or affecting a safety system. That's not a reason to avoid improvement, but it is a reason to plan changes deliberately and not treat OT like “faster-moving IT.”
Asset lifespan and mixed-era environments
IT infrastructure follows a predictable refresh cycle (typically three to five years). OT doesn't work that way.
Legacy controllers and "never-touch" systems routinely coexist with modern devices, sometimes on the same network segment. A controller installed 15 years ago may still be running a critical process, and that's not going away anytime soon. The design has to account for that reality.
Physical and environmental conditions
Enterprise networks live in controlled environments: data centers, server rooms, structured cabling runs. Industrial environments are a different world: extreme temperatures, vibration, dust, electrical noise, hazardous area classifications, limited cabinet space.
Infrastructure class (industrial-rated vs. commercial-grade) is an architectural decision, not a procurement detail. Installing the wrong hardware in the wrong environment doesn't always cause an immediate failure. But, it creates intermittent problems that are difficult to trace and expensive to fix.
Find best practices for OT network design here >>>
Traffic Behavior: Where OT Breaks IT Assumptions
This is one of the most common places IT thinking creates problems in OT environments, but it’s one of the least obvious.
In IT networks, the primary traffic concern is usually bandwidth. Can the network move enough data, and quickly? In OT environments, the more important questions are often about latency and jitter. Control systems depend on predictable communication timing. A switch architecture that introduces variable latency, or a segment overwhelmed by broadcast traffic, can affect how a controller responds, even if the network technically “works” by every other measure.
Many industrial protocols rely on broadcast or multicast communication. That's not inherently a problem, but it has to be understood and accounted for in the design. In a flat or loosely segmented network, broadcast traffic from one area of the plant can affect unrelated systems on the other side of the facility.
One misconfigured device can amplify broadcast traffic across a large portion of the environment. The result? Devices that stop responding for no obvious reason. Nothing is physically broken. The network just wasn't structured to contain the impact.
Here’s the bottom line: Where traffic can go matters as much as how much traffic can flow. Store-and-forward vs. cut-through switching, ring vs. star topologies, where redundant paths terminate—these decisions affect how the network behaves under normal load and how it responds when something goes wrong.
How OT and IT Networks Are Typically Structured
The structural difference between OT and IT networks directly reflects their different purposes.
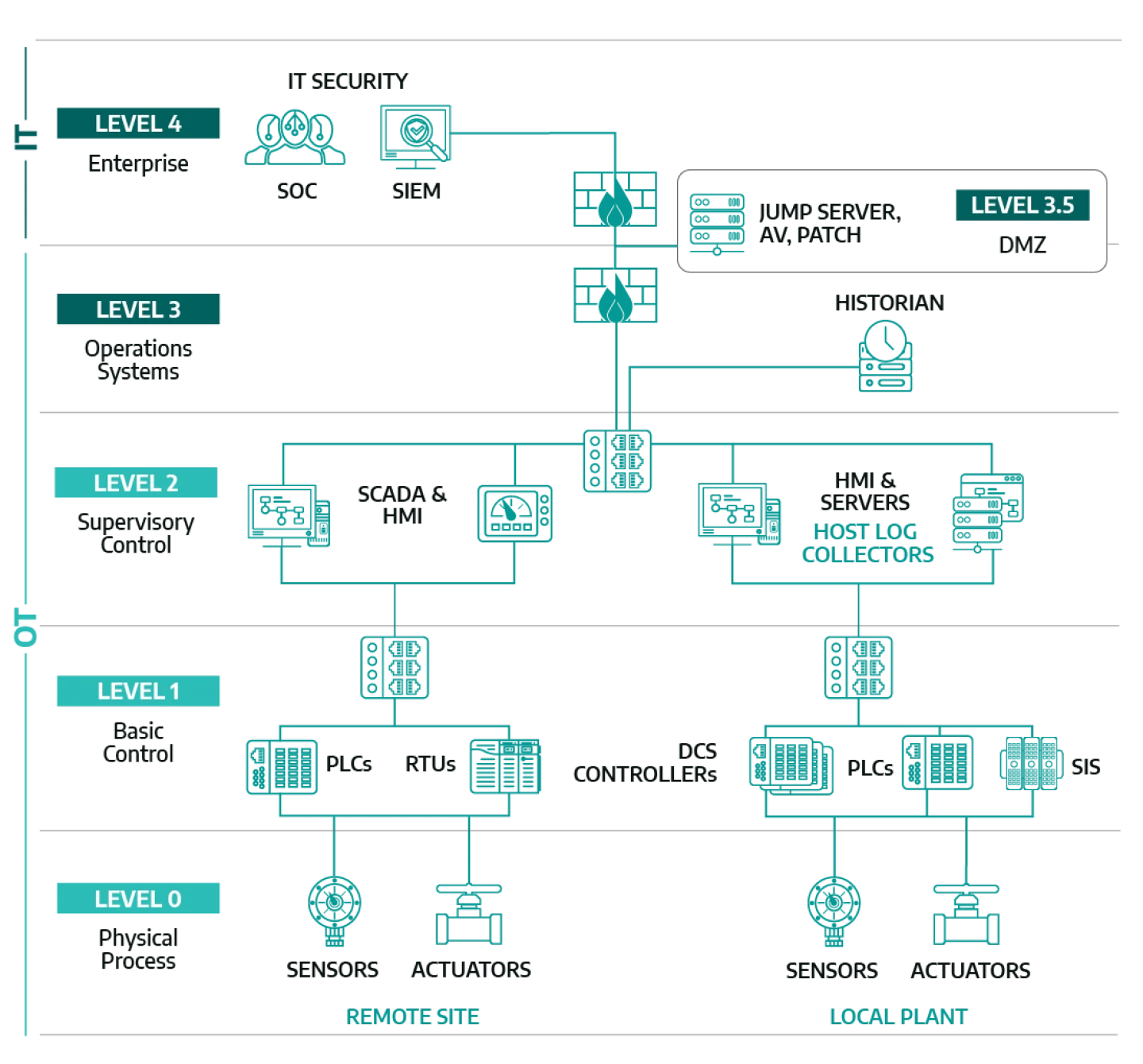
Image from Dragos
IT networks are organized around users and business functions, typically using a campus or core-distribution-access model that connects people to centralized services and applications. Segmentation usually follows department or business unit lines. It's designed for flexibility and broad access.
OT networks are organized around operational functions, critical processes and containment. The common framework is cell/area zones grouped into process networks, with boundaries defined by what systems need to talk to each other and what the consequences are if those communications get disrupted. A well-designed OT architecture makes it clear which systems belong together, which boundaries control traffic between zones, and how problems are less likely to spread beyond intended boundaries.
The core distinction: IT architecture connects people to resources, while OT architecture structures how equipment communicates to support production with a focus on safety and reliability. Those are different problems that require different solutions.
Security Differences: Tools vs Architecture
The approach to security in OT environments is fundamentally different from enterprise IT, and confusing the two is one of the more common mistakes we see.
IT security often starts with identity and endpoint controls. Managed devices, user authentication, endpoint agents, and centralized policy enforcement all work well when devices are known, updatable, and under IT control.
OT security starts with architecture and boundaries. Many OT assets (controllers, sensors, older HMIs) can't run agents, can't be patched on a regular cycle, and were never designed with modern security assumptions in mind. In these environments, segmentation, controlled communication paths, and structured remote access can’t be security add-ons. They're the foundation everything else has to be built on.
That distinction matters more than most people realize. In OT, security is often an outcome of architecture before it's a product stack. Adding security tools to a flat, poorly segmented network doesn't fix the underlying exposure. It just gives you better visibility into a structure that still lets problems travel freely.
What Goes Wrong When IT Thinking Drives OT Design
These differences aren't theoretical. They play out in predictable failure patterns that show up repeatedly in industrial environments.
Flat or overly permissive networks create conditions where a single event like a broadcast storm, a switching loop, or a misbehaving device can disrupt communication across large portions of the plant. Without defined boundaries, there's no containment. What should be a localized problem becomes a production event.
Remote access sprawl develops when connectivity gets added to solve immediate support needs without a structured access model. Vendors need access. Integrators need visibility. Temporary solutions become permanent. Over time, multiple unmanaged pathways accumulate, and it becomes genuinely unclear who can reach what, and from where. That's both an operational risk and a security problem.
"Add a tool" approaches don't fix architecture debt. Layering monitoring systems, security appliances, or additional hardware onto a network with foundational design gaps doesn't resolve those gaps. It adds complexity to an already fragile structure and makes the next problem harder to trace.
Undocumented dependencies turn routine changes into unpredictable events. When the teams who built the network move on, devices stay connected long after their original purpose is forgotten. Changes introduce unexpected side effects because nobody can fully describe what the network actually does.
If you're not sure which of these patterns exist in your environment, that uncertainty itself is worth paying attention to. Schedule a quick network assessment here >>>
How IT and OT Can Actually Work Together
The goal here isn't permanent separation. Modern industrial operations increasingly require IT/OT integration for data initiatives, remote operations, and production visibility. The question is how to do it without creating instability in the process.
A few things tend to determine whether that collaboration goes well:
- Start with shared goals, not competing standards. Uptime, safety, risk containment, and maintainability are things both sides care about. Starting from shared objectives is more productive than debating whose standards apply.
- Define ownership explicitly. Who owns switching and routing decisions? Who sets the firewall policy? Who governs remote access? Who maintains documentation? Ambiguous ownership is one of the most consistent sources of both security gaps and operational friction. Spelling it out clearly reduces both.
- Build a roadmap that respects how operations actually work. Improvement in OT environments has to happen in phases, aligned with maintenance windows, structured to avoid disrupting active production. "Rip and replace" almost never works here—and it doesn't have to. Thoughtful, incremental changes can move an environment a long way without introducing new risk.
When an OT Network Assessment Makes Sense
Most industrial networks weren't designed all at once. They grew. A machine added here, a switch installed there, remote access enabled when someone needed it. That's all normal. What that evolution tends to produce, though, is architecture that's hard to describe clearly from the inside.
Here’s where we’ve seen assessments be valuable:
- Recurring issues that never fully resolve. Troubleshooting might address symptoms, but the root cause returns under load or during peak production.
- Modernization efforts keep stalling. New systems, IIoT initiatives, or remote site expansions are on the table, but nobody can confidently say how those changes will affect what's already running
- Limited or outdated documentation is all that exists. Device counts are estimates, segmentation is assumed rather than verified, or remote access paths have accumulated without a clear map.
- Failures spread further than expected. An outage or broadcast event reveals structural weaknesses that weren't visible until something actually went wrong
In each case, the underlying need is the same: a clear picture of how the network is actually built and how it behaves—not how it was intended to work. A structured assessment maps the current state, identifies the architectural gaps, and defines a prioritized path forward based on operational reality rather than best guesses.
Common Questions
Isn't OT just IT on the plant floor?
While OT shares some of the same underlying technology, the design goals, constraints, and failure consequences are fundamentally different from IT. OT exists to support production, not users. That changes everything about how the network should be built and maintained.
Can we improve without replacing everything?
Yes, and that's usually how it should happen. Most OT network improvements are incremental and phased to align with maintenance windows. The goal is to close structural gaps without disrupting active operations.
How do you secure vendor remote access in OT environments?
We help customers structure vendor remote access by designing pathways intentionally rather than letting them accumulate. Structured remote access means defined, auditable entry points, time-limited sessions, and access scoped to specific systems, not open-ended connectivity to the broader network.
What's the first step if we don't even have accurate network diagrams?
That's exactly what an assessment is designed to address. Starting with a current-state discovery (physical topology, device inventory, traffic behavior, segmentation boundaries) gives you the foundation to make any meaningful improvement from there.
Not sure where your OT network actually stands? INS conducts structured OT network assessments that map the current architecture, surface the gaps, and define a clear path toward scalable, manageable, reliable operations.



